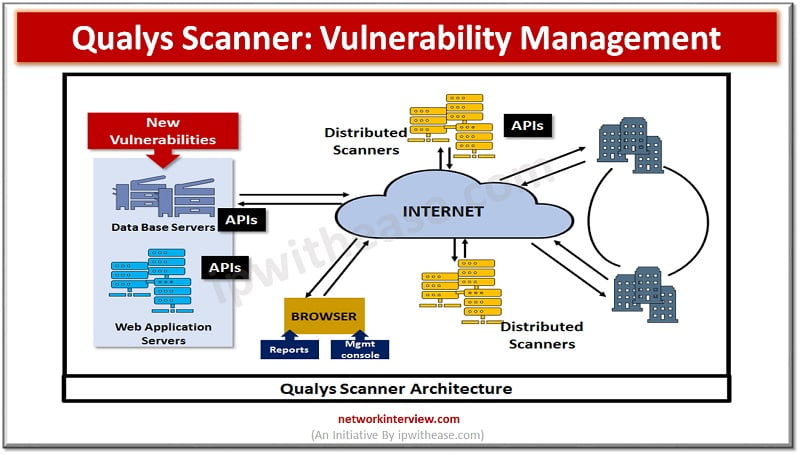
How to Configure NetScaler Application Firewall Signatures Protection Based on Vulnerability Scan Result of QualysGuard

How to Configure NetScaler Application Firewall Signatures Protection Based on Vulnerability Scan Result of QualysGuard
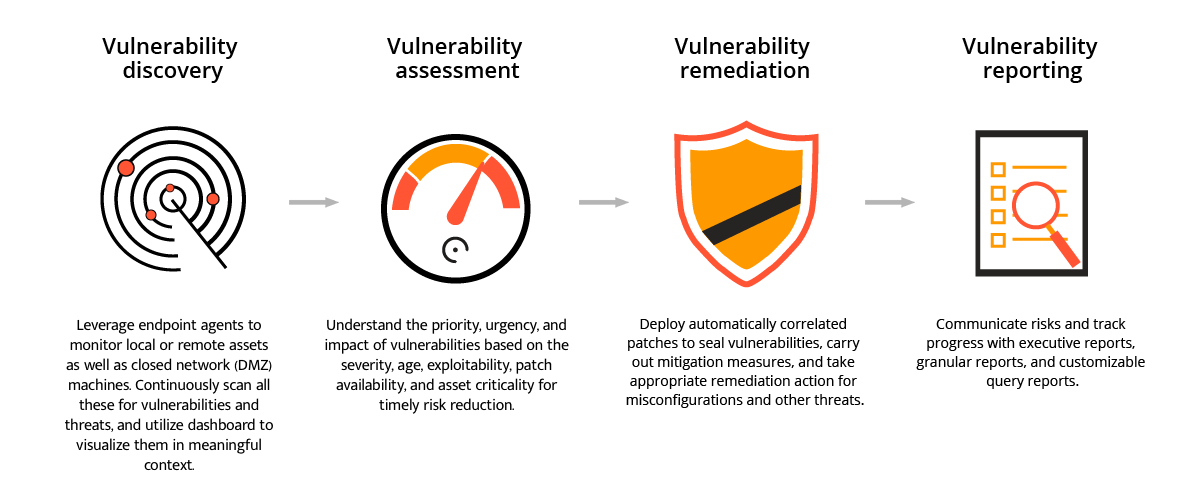
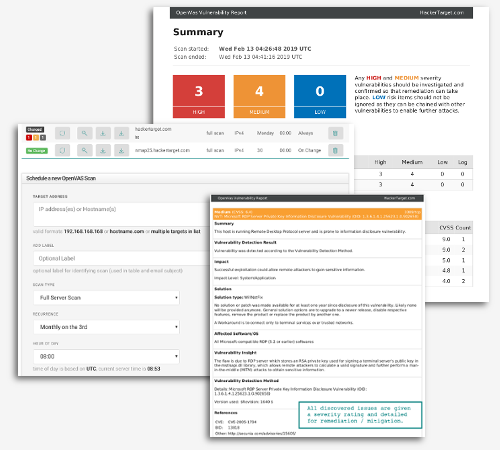
Vulnerability Scanner | Powerful Vulnerability Scanning Tools - ManageEngine Vulnerability Manager Plus